KMSキーで暗号化しているS3を他アカウントのEC2が使用できるようにする
・KMSキーで暗号化しているS3に他アカウントからアクセスしたい
KMSキーで暗号化しているS3にアクセスしようとすると、KMSキーの暗号化が行われていないため、アクセス拒否される場合があります。
今回はKMSキーで暗号化されているS3にアクセスできる方法を紹介します。
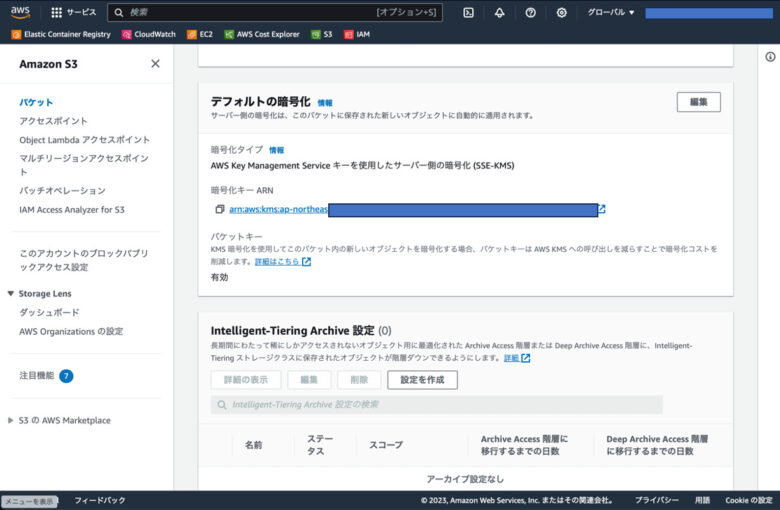
前提条件
KMSキーで暗号化したS3作成済み
最初のKMSキーポリシー
KMSキーポリシーには下記が設定されています。
{
"Id": "key-consolepolicy-3",
"Version": "2012-10-17",
"Statement": [
{
"Sid": "Enable IAM User Permissions",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::AWS_ACCOUNT_1:root"
},
"Action": "kms:*",
"Resource": "*"
},
{
"Sid": "Allow access for Key Administrators",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::AWS_ACCOUNT_1:user/mikiadmin"
},
"Action": [
"kms:Create*",
"kms:Describe*",
"kms:Enable*",
"kms:List*",
"kms:Put*",
"kms:Update*",
"kms:Revoke*",
"kms:Disable*",
"kms:Get*",
"kms:Delete*",
"kms:TagResource",
"kms:UntagResource",
"kms:ScheduleKeyDeletion",
"kms:CancelKeyDeletion"
],
"Resource": "*"
},
{
"Sid": "Allow use of the key",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::AWS_ACCOUNT_1:user/mikiadmin"
},
"Action": [
"kms:Encrypt",
"kms:Decrypt",
"kms:ReEncrypt*",
"kms:GenerateDataKey*",
"kms:DescribeKey"
],
"Resource": "*"
},
{
"Sid": "Allow attachment of persistent resources",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::AWS_ACCOUNT_1:user/mikiadmin"
},
"Action": [
"kms:CreateGrant",
"kms:ListGrants",
"kms:RevokeGrant"
],
"Resource": "*",
"Condition": {
"Bool": {
"kms:GrantIsForAWSResource": "true"
}
}
}
]
}S3バケットポリシー
設定されているS3バケットポリシーは下記の通りです。(他アカウントからのアクセス許可設定済み)
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "Example",
"Effect": "Allow",
"Principal": {
"AWS": [
"arn:aws:iam::ANOTHER_AWS_ACCOUNT_2:role/anothes3-access-policy",
"arn:aws:iam::ANOTHER_AWS_ACCOUNT_3:role/AnotherS3_Access_Role"
]
},
"Action": [
"s3:PutObject",
"s3:ListBucket"
],
"Resource": [
"arn:aws:s3:::ec2-access-test-miki",
"arn:aws:s3:::ec2-access-test-miki/*"
]
}
]
}KMSポリシーの修正
KMSポリシーに他アカウントからの使用を許可するように、下記を追加します。
{
"Sid": "Allow an external account to use this KMS key tempolary",
"Effect": "Allow",
"Principal": {
"AWS": [
"arn:aws:iam::ANOTHER_AWS_ACCOUNT_2:role/anothes3-access-policy",
"arn:aws:iam::ANOTHER_AWS_ACCOUNT_3:role/AnotherS3_Access_Role"
]
},
"Action": [
"kms:Encrypt",
"kms:Decrypt",
"kms:ReEncrypt*",
"kms:GenerateDataKey*",
"kms:DescribeKey"
],
"Resource": "*"
}以上です。KMSキーの許可にアクセスしてくるS3用ロールを付与するだけでできました。
ちなみに、全体のKMSキーポリシーは下記のようになりました。
{
"Version": "2012-10-17",
"Id": "key-consolepolicy-3",
"Statement": [
{
"Sid": "Enable IAM User Permissions",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::AWS_ACCOUNT_1:root"
},
"Action": "kms:*",
"Resource": "*"
},
{
"Sid": "Allow access for Key Administrators",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::AWS_ACCOUNT_1:user/mikiadmin"
},
"Action": [
"kms:Create*",
"kms:Describe*",
"kms:Enable*",
"kms:List*",
"kms:Put*",
"kms:Update*",
"kms:Revoke*",
"kms:Disable*",
"kms:Get*",
"kms:Delete*",
"kms:TagResource",
"kms:UntagResource",
"kms:ScheduleKeyDeletion",
"kms:CancelKeyDeletion"
],
"Resource": "*"
},
{
"Sid": "Allow use of the key",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::AWS_ACCOUNT_1:user/mikiadmin"
},
"Action": [
"kms:Encrypt",
"kms:Decrypt",
"kms:ReEncrypt*",
"kms:GenerateDataKey*",
"kms:DescribeKey"
],
"Resource": "*"
},
{
"Sid": "Allow attachment of persistent resources",
"Effect": "Allow",
"Principal": {
"AWS": "arn:aws:iam::AWS_ACCOUNT_1:user/mikiadmin"
},
"Action": [
"kms:CreateGrant",
"kms:ListGrants",
"kms:RevokeGrant"
],
"Resource": "*",
"Condition": {
"Bool": {
"kms:GrantIsForAWSResource": "true"
}
}
},
{
"Sid": "Allow an external account to use this KMS key tempolary",
"Effect": "Allow",
"Principal": {
"AWS": [
"arn:aws:iam::ANOTHER_AWS_ACCOUNT_2:role/AnotherS3_Access_Role",
"arn:aws:iam::ANOTHER_AWS_ACCOUNT_2:role/anothes3-access-policy"
]
},
"Action": [
"kms:Encrypt",
"kms:Decrypt",
"kms:ReEncrypt*",
"kms:GenerateDataKey*",
"kms:DescribeKey"
],
"Resource": "*"
}
]
}以上です。誰かの参考になれば幸いです。
